Sophos XG Firewall Vulnerability
Hackers have been targeting Sophos XG Firewall due to the Zero-Day exploit that allows hackers to inject the Asnarok Malware.
Sophos said in their blog. “The attack affected systems configured with either the administration interface (HTTPS admin service) or the user portal exposed on the WAN zone. In addition, firewalls manually configured to expose a firewall service (e.g. SSL VPN, SPX Portal) to the WAN zone that shares the same port as the admin or User Portal were also affected.”
What was compromised?
It was found that the data impacted on the firewall was all local usernames and hashed passwords of any local user accounts. This would mean, local device admins, user portal accounts, and accounts used for remote access. However the passwords associated with external authentication like Active Directory (AD) or LDAP were not compromised.
Have I been compromised?
Well Sophos best practice is to make sure the firewall firmware is updating automaticlly so we hope that a patch was pushed to your firewall before falling victum to the Sophos XG Firewall Vulnerability.
To ensure that you receive the hotfix.
If you have disabled “Allow automatic installation of hotfixes”, please reference the following KBA for instructions on how to apply the required hotfix: https://community.sophos.com/kb/en-us/135415
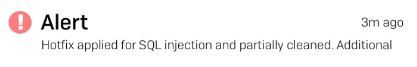
If you are not compromised you will see this alert.
If you are compomised you see that your firewall is partially cleared.
Once the hotfix is applied.
For uncompromised XG Firewall devices, no additional steps are required.
For compromised XG Firewall devices that have received the hotfix, we strongly recommend the following additional steps to fully remediate the issue:
- Reset device administrator accounts
- Reset passwords for all local user accounts
- Although the passwords were hashed, it is recommended that passwords are reset for any accounts where the XG credentials might have been reused.
- Fixing WebView2 Issues on ARM64: Why Outlook and Teams Keep Breaking (and How to Fix Them)
- How to Enable Auto Recording & Transcription in Microsoft Teams and Assign Meeting Policies to All Users
- How to Install SentinelOne on Ubuntu 24.04
- How to Completely Remove SentinelOne from Ubuntu 24.04
- PowerShell Script to Force Uninstall Umbrella Roaming Client
Discover more from Patrick Domingues
Subscribe to get the latest posts sent to your email.